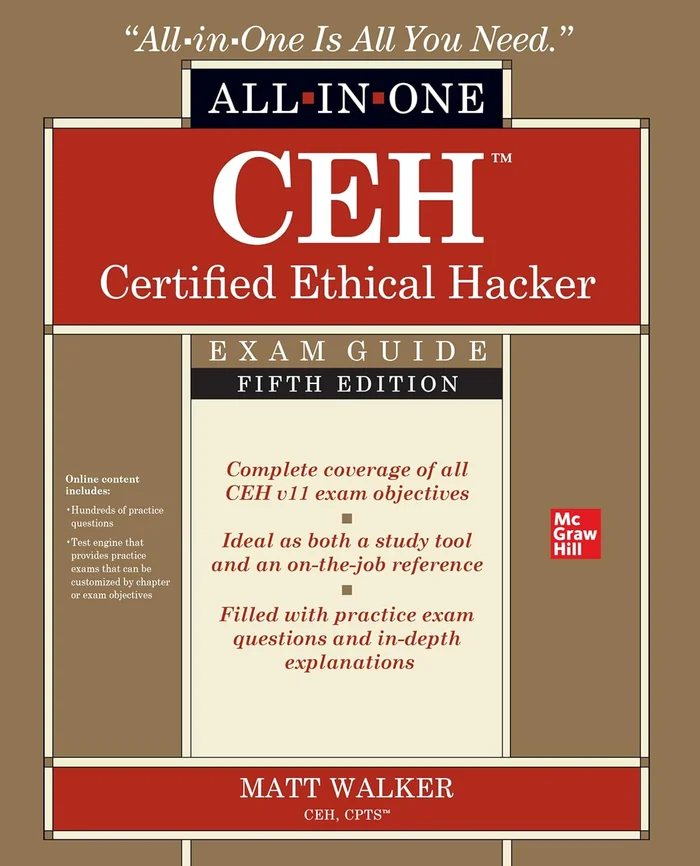
Description
Ethical hacking fundamentals
Reconnaissance and footprinting
Scanning and enumeration
Sniffing and evasion
Attacking a system
Hacking web servers and applications
Wireless network hacking
Mobile, IoT, and OT
Security in cloud computing
Trojans and other attacks, including malware analysis
Cryptography
Social engineering and physical security
Penetration testing


Reviews
There are no reviews yet.